|Author- Hency Kushwah|
Image: Self Created
This is not a rumor. It is policy. India’s messaging ecosystem is about to change.
From March 1, 2026, popular apps such as WhatsApp, Telegram, Signal, Snapchat, ShareChat, and others will be required to comply with a new government directive mandating SIM binding — meaning these apps will function only if the registered SIM card is physically present and active in the user’s device.
The move, directed by the Department of Telecommunications (DoT), marks one of the most significant regulatory interventions in India’s digital communication landscape in recent years.
Key Outlooks
- SIM Binding Becomes Mandatory from March 1, 2026: Messaging apps must ensure the registered SIM remains active and physically present in the user’s device.
- Shift from OTP-Only Model: Unlike the earlier system where SIM was required only for initial verification, continued access will now depend on ongoing SIM validation.
- Government’s Position: The measure is aimed at enhancing traceability and curbing cyber fraud linked to inactive or recycled SIM numbers.
- Regulatory Debate: Industry bodies argue that OTT messaging platforms are being subjected to telecom-style compliance beyond their traditional regulatory classification.
- User Impact at Scale: With over 500 million WhatsApp users in India, even minor operational friction could affect millions daily.
- Unanswered Policy Question: Whether SIM binding addresses root-level cybercrime structures or primarily strengthens identity traceability remains to be tested.
What Exactly Is Changing?
Until now, WhatsApp required a SIM only for initial OTP verification. After registration, users could remove the SIM, use Wi-Fi, operate linked devices, and continue accessing services without interruption.
That changes on March 1. Under the new compliance structure:
- The registered SIM must remain active and physically present.
- Messaging services may disable access if the SIM is removed or deactivated.
- Multi-device features may require periodic re-authentication.
- Linked desktop/web sessions could auto-log out to ensure SIM verification continuity.
In simple terms- no active SIM, no messaging access.
Why the Government Says It’s Necessary?
The government’s justification centers on cybersecurity and fraud prevention.
Officials have pointed to the surge in SIM-based financial scams, OTP fraud, impersonation using inactive or recycled numbers and bot not limited to, messaging platforms being used for organized cybercrime
Communications Minister Jyotiraditya Scindia has reportedly made it clear that the deadline will not be extended. According to official reasoning, traceability must align with India’s telecom identity framework, where every SIM is KYC-verified.
The logic is straightforward that if SIMs are tightly regulated, messaging identities should also be tied to them. The government frames this as strengthening digital accountability and not limiting freedom.
The Industry Pushbacks: The announcement has not gone uncontested. The Broadband India Forum (BIF), an industry body representing technology and broadband stakeholders, has urged the DoT to reconsider aspects of the new rule. The argument from industry is twofold:
1. Messaging apps are not telecom operators.
2. Binding them to telecom-style compliance may exceed regulatory intent.
Technology platforms traditionally operate under IT regulations, not telecom frameworks. Critics argue that imposing telecom-style obligations on OTT (over-the-top) platforms could blur legal boundaries.
Operational concerns are also being raised:
- International travelers switching SIMs frequently
- Business users managing multiple devices
- Users relying on secondary devices or tablets
- Rural connectivity fluctuations are affecting verification stability
For millions of Indians, WhatsApp is not just an app, it is infrastructure. Any disruption becomes a systemic issue. For the average user, the impact may not be immediate but it will be noticeable.
If your SIM expires, is suspended, or is physically removed, you may lose access to your messaging account until re-verification.
Frequent SIM swaps? Expect repeated authentication.
Using WhatsApp Web without your phone nearby? That experience may become less seamless.
India has over 500 million WhatsApp users. Even minor friction scales massively.
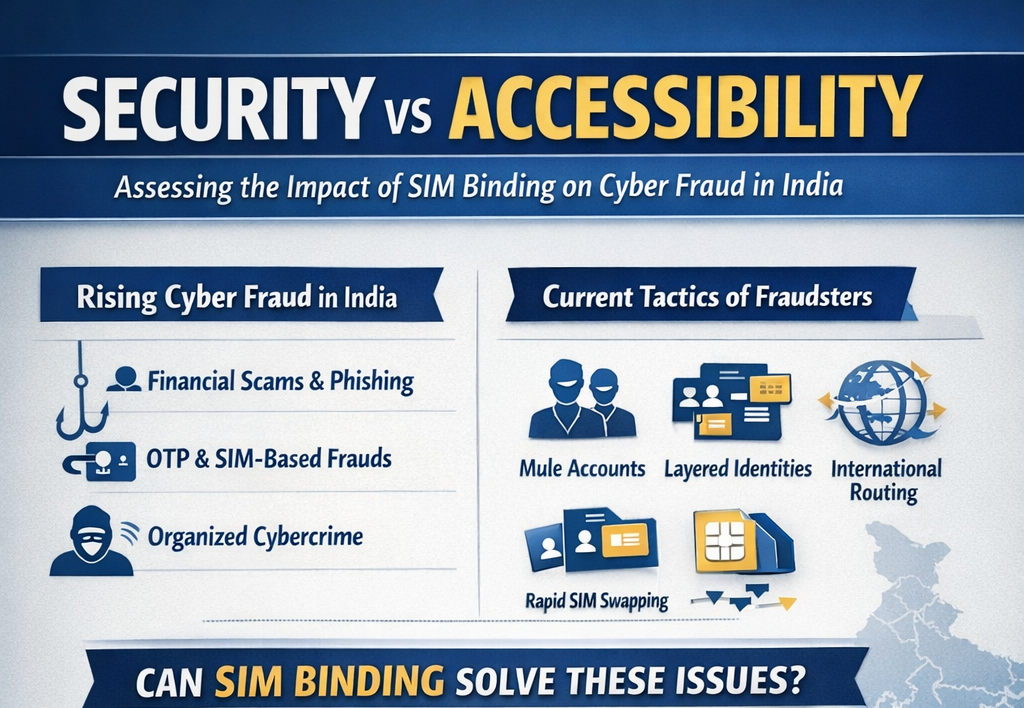
Security vs Accessibility
India has witnessed a significant rise in cyber-enabled financial fraud over the past few years. Data released by the Ministry of Home Affairs (MHA) and reflected on the National Cyber Crime Reporting Portal (NCRP) indicates a steady increase in complaints relating to online financial scams, phishing attacks, OTP-based fraud, impersonation calls, and messaging-linked financial deception.
According to parliamentary responses and official briefings in recent years, cyber fraud cases have grown both in volume and complexity. The Indian Cyber Crime Coordination Centre (I4C) has repeatedly flagged the increasing use of digital messaging platforms and internet-based calling systems in executing fraud schemes. Law enforcement agencies have noted that fraudsters frequently rely on Fraudulent SIM cards obtained through identity misuse, recycled or dormant numbers reactivated for short-term exploitation, OTP interception through social engineering, and messaging platforms to circulate malicious links or impersonate officials.
The government’s SIM binding mandate is positioned as an additional layer of identity continuity. Because telecom SIM cards in India are issued through KYC verification under the Department of Telecommunications’ regulations, linking active SIM presence to messaging platforms is intended to reduce misuse of inactive or swapped numbers.
However, cybercrime investigations conducted by enforcement agencies suggest that sophisticated fraud networks often operate through more complex mechanisms than single-device misuse.
Investigative reports from state cyber cells and central agencies indicate that organized fraud syndicates frequently employ:
- “Mule accounts,” i.e., bank accounts opened in the names of third parties to launder stolen funds,
- Layered identity chains where one individual acquires SIMs, another operates messaging, and a third handles financial withdrawals,
- Cross-border routing of digital traffic using VPNs and VoIP systems,
- Rapid SIM churn- activating and discarding SIM cards within short time windows,
- Offshore call centers operating outside Indian jurisdiction.
In several high-profile cybercrime crackdowns, authorities have found that messaging accounts used for fraud were often created with valid KYC SIMs, but controlled by organized networks rather than individual users. This indicates that traceability mechanisms, while useful for investigation, may not automatically dismantle structured cybercrime operations.
SIM binding strengthens attribution by tying messaging access to an active telecom identity. Whether it materially enhances preventive disruption depends on the broader enforcement architecture, including banking safeguards, transaction-monitoring systems, inter-agency coordination, and cross-border cooperation.
Another practical dimension relates to identity recycling. Telecom operators periodically reassign unused numbers after deactivation. Fraud investigations have revealed instances where messaging accounts linked to previously assigned numbers were exploited during transition windows. Mandatory active SIM verification may reduce such vulnerabilities by requiring continuous authentication.
At the same time, cybersecurity specialists emphasize that organized fraud ecosystems adapt quickly to regulatory changes. When one operational pathway becomes constrained, alternate methods often emerge, including overseas SIM procurement, virtual number systems, or synthetic identity creation.
These questions are operational, not theoretical. Their answers will emerge through enforcement data, reported fraud statistics, and implementation outcomes in the months following rollout.
The existence of cyber fraud is established and documented. The effectiveness of SIM binding as a structural deterrent, however, will depend on how it interacts with India’s broader cybersecurity, banking, telecom, and digital governance frameworks.
Final Word
This is not the end of WhatsApp. It is a structural shift in how it functions within India. Security concerns are real. Cyber fraud is real. Regulatory intervention is understandable. But so are concerns about regulatory overreach, operational complexity, and long-term implications for platform governance.
On March 1 this will be rolled out. It is a test of how India balances security, convenience, regulation, and digital autonomy in the world’s largest messaging market. The real story will unfold not in policy notes, but in how millions of users experience this change.